Click the “Google Sign in” button to be directed to the Google Sign-in page.
Accounts will be locked out or suspended temporarily if too many invalid login attempts are detected. By default, many devices are set to automatically connect to known wireless networks (like FITAIR). If you change your FIT password you must update the devices connect to FITAIR with your new password. Learn how to update your wireless devices with your new/current password.
This article is related to:
Many of us store so much of our information on our mobile devices from photos to phone numbers (do you know your best friend’s number by heart?) that we feel uneasy when we don’t have it. That feeling can be amplified if our phone is lost or stolen. Best practices to be Cybersafe is to […]
Campus printing is available in multiple locations at FIT. However, some students choose to bring a personal printer for their use in the Residence Halls. If you are buying a printer, please keep in mind that wireless printers do not work on the FIT wireless network. Please make sure that the printer has a way […]
iOS To sign in, add your account You can add both Gmail and non-Gmail accounts to the Gmail app on your iPhone or iPad. On your iPhone or iPad, open the Gmail app . In the top right, tap your profile picture. Tap Add another account. Choose the type of account you want to add: If you use […]
Use the menu on the right to jump to the instructions for your device. Viewing these instructions on a mobile device, click on the tab on the right to display the menu. How to Connect iOS Follow the instructions below when connecting to FITAIR for the first time on your iOS device. If you were […]
This article is related to:
To register a device to the Wired Network at FIT, you will need to find the device’s MAC Address. You may register up to three compatible devices to the Wired Network when you are on campus; you will not be able to register devices when you are off-campus. Once a device is registered, it will automatically connect to the FIT […]
This article is related to:
As a public institution in New York State where Freedom of Information laws are broad, FIT is legally required to review and produce documents and data—including email—at the public’s request, regardless of the purpose of the request, with limited exceptions. FIT is subject to review by any number of agencies charged with enforcing certain legal […]
This article is related to:
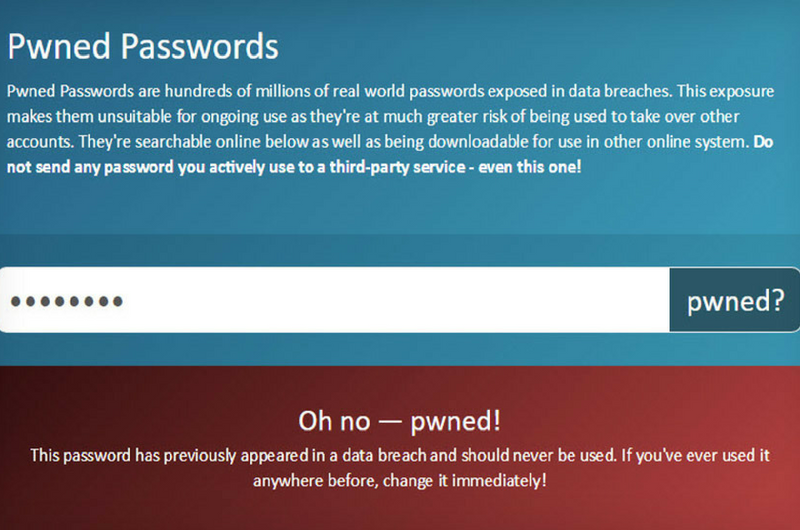
Have you ever wondered if your account information or password has ever been exposed in a data breach? Have I Been PWNED? (HIBP) is a free resource developed by a Microsoft researcher for anyone to quickly assess if they may have been put at risk due to an online account of theirs having been compromised or […]
1. Sign in to your FIT Gmail account 2. Select “All Mail” on the left-hand side (under the compose button). Note: The order of the items displayed in your inbox can be customized. Therefore, depending on how you have organized your Gmail, you may need to select "More" to display "All Mail"
This article is related to:
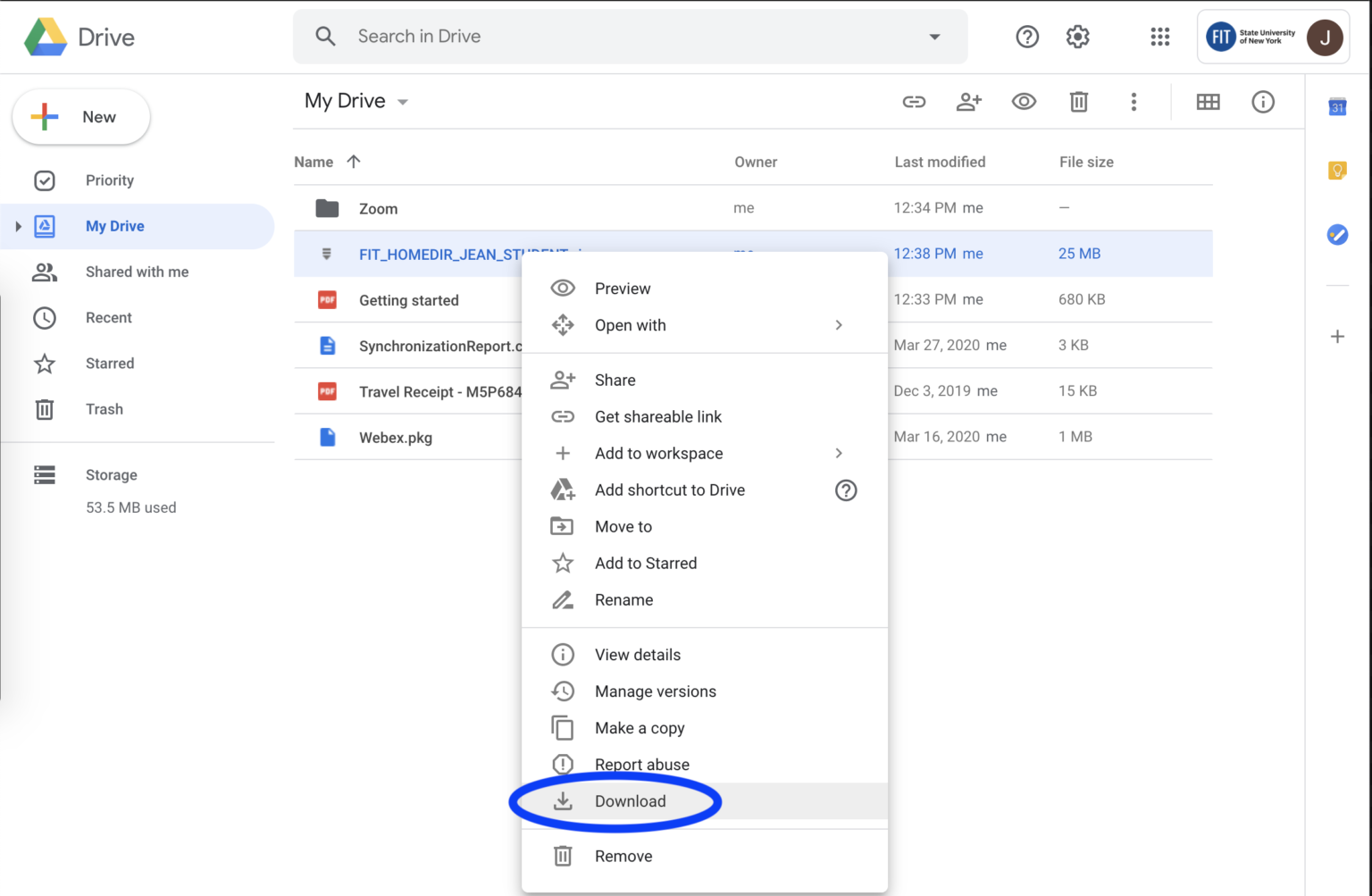
In mid-2020, the Division of Information Technology began the final phase of a project to retire Home Directories—the networked personal storage space for students only accessible from workstations on the FIT campus. The Home Directory is sometimes referred to as the N Drive, Y Drive, or Campus Drive. Once you see your Home Directory zip […]
IMPORTANT: Protect Privacy and Intellectual Property Use of AI through non-enterprise accounts may result in public data exposure. FIT bears no responsibility whatsoever for potential claims or losses resulting from individuals entering, posting, sharing and/or linking their intellectual property or copyrighted content to or in either a public generative-AI text prompt, such as the consumer […]
This article is related to:
IMPORTANT: Protect Privacy and Intellectual Property Use of AI through non-enterprise accounts may result in public data exposure. FIT bears no responsibility whatsoever for potential claims or losses resulting from individuals entering, posting, sharing and/or linking their intellectual property or copyrighted content to or in either a public generative-AI text prompt, such as the consumer […]
IMPORTANT: Protect Privacy and Intellectual Property Use of AI through non-enterprise accounts may result in public data exposure. FIT bears no responsibility whatsoever for potential claims or losses resulting from individuals entering, posting, sharing and/or linking their intellectual property or copyrighted content to or in either a public generative-AI text prompt, such as the consumer […]
1. Go to https://calendar.google.com Tip! If you need to record or transcribe a meeting, contact the meeting organizer before the meeting so they can make you a co-host. Only the Host/Co-host with the correct subscription rights can use the recording and transcription features. 1. Navigate to https://calendar.google.com 2. Right-click on the meeting you want to modify, […]
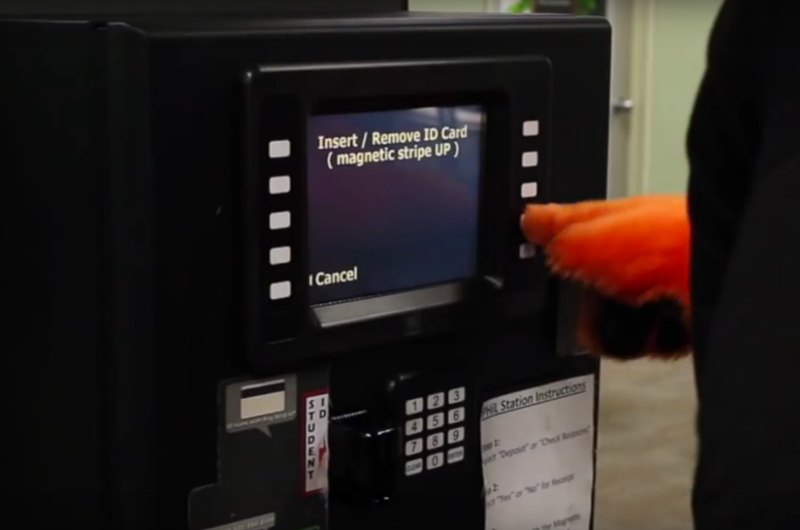
Learn how to add money to your Campus Card online using the eAccounts system.
This article is related to:
Security Recommendation The Microsoft Authenticator app provides the strongest protection for your account, and it should remain your primary sign-in method. With the app’s default settings, you must unlock your phone and confirm the request, which creates a built-in layer of security that other methods cannot match. While adding a backup option is helpful, adding […]
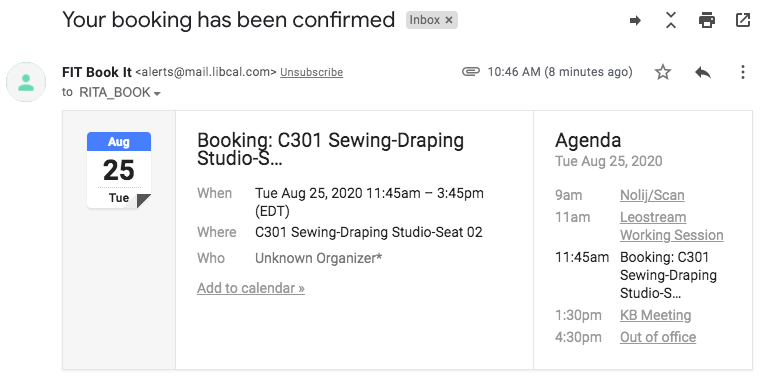
Reservations Suspended FIT Book It reservations end on November 25. All courses and classes will be fully remote, and students will no longer have access to campus studios and labs. Included in your email confirmation there will be a custom link to cancel your booking. Click on the link included in the confirmation email. The […]
This article is related to:
G Suite for Education offers a multitude of security features including allowing you to monitor how your account is being accessed through the Activity Information panel. This is one of the easiest ways for you to ensure that your account isn’t being accessed without your permission. "The Activity Information Panel" allows you to check what browser, […]
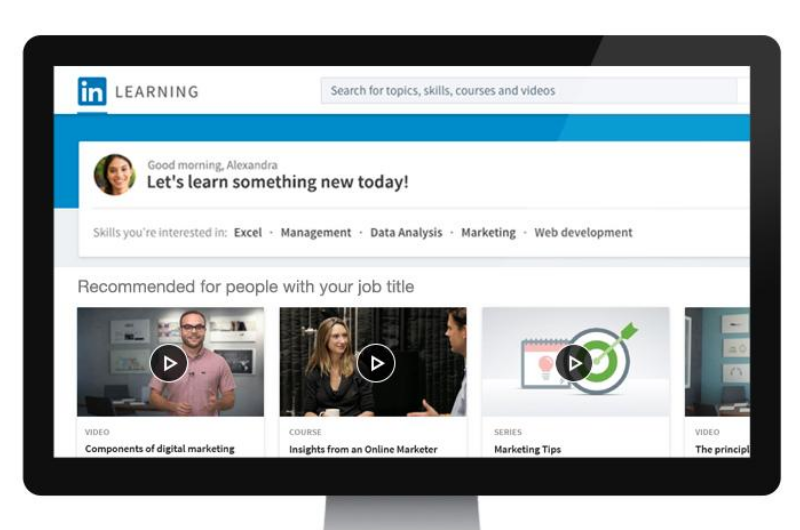
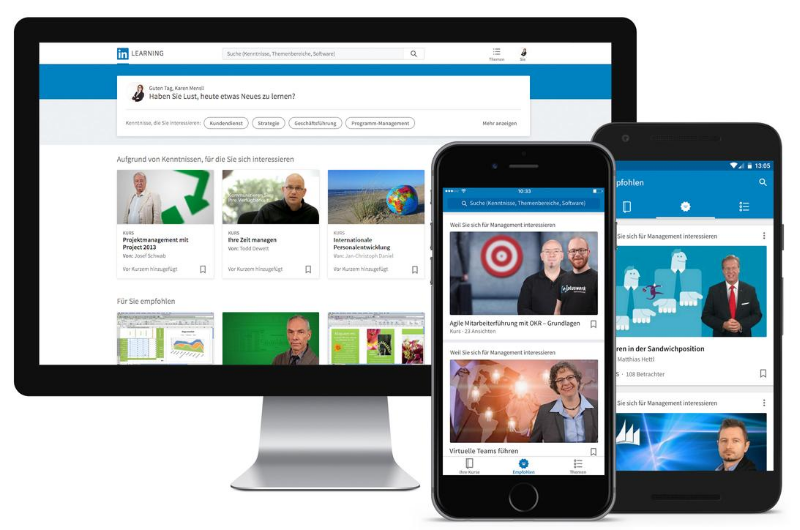
When you connect your LinkedIn account, only your learning activity and profile information (name, title, profile photo) are shared with FIT LinkedIn Learning account administrators. To begin, go to https://www.linkedin.com/learning and click the “Sign in” button in the top right hand corner of the page. Enter your FIT email address and click the “Continue” button. […]
This article is related to:
TLDR (Article Summary) Passphrases are a simple and effective way to secure your accounts. By combining meaningful words into a long, unique, and complex phrase, you can create something that’s easy for you to remember but hard for others to guess. Following this checklist can help you create a strong, unique passphrase. At least 15 […]
If you believe your FIT is lost or stolen, the first thing you need to do is deactivate the card. Everyone has the ability to deactivate their card blocking access to meal plan funds and Fashion Express funds. Follow our instructions on how to deactivate your FIT ID card. 1. Go to https://fit-sp.blackboard.com/eaccountsAlternatively, you may […]
If you wish to disconnect your profile due to privacy concerns, please note that even when the profile is connected to your LinkedIn Learning account, FIT can only see your LinkedIn profile picture and the information you’ve set to public. If you still wish to disconnect your Learning license from your LinkedIn profile, please: Log […]
This article is related to:
Chrome, Firefox, Safari, Edge, Opera, and Internet Explorer 8 or later. For the widest compatibility with Duo's authentication methods, we recommend recent versions of Chrome and Firefox.
This article is related to:
How do I do a search for mail older than a certain date?There is a long list of advanced search operators that you can use in Gmail. The list can be found here. One of the most powerful ones is to search for messages by date and here is how it is done:The search box is at the […]
A media access control address (MAC address), unique identifier for your device connecting to a network, sometimes called physical address. An Internet Protocol address (IP Address), is a unique string of numbers separated by periods that identifies each computer over a network. You will need to know how to obtain your MAC address to register […]
By default, many devices are set to automatically connect to known wireless networks (like FITAIR). If you change your FIT password you must update the devices connect to FITAIR with your new password. If you neglect to take this step your devices will attempt to automatically connect to FITAIR with an invalid password causing your […]
This article is related to:
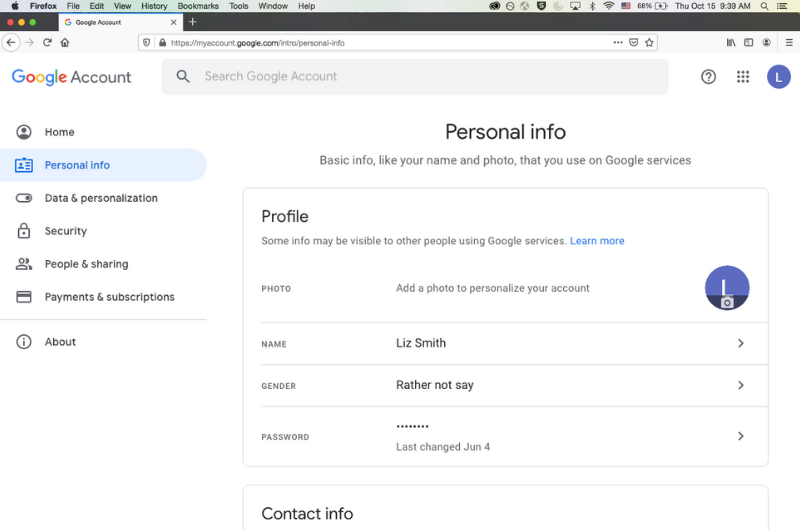
You may have your chosen first name display for Google Meet, Gmail, and other G Suite apps by changing your Google Profile name. Changing your Google Profile name has these benefits: It creates a DISPLAY NAME in all caps across many key locations within the Google suite. While the FIT email address will continue to display […]
This article is related to:
Learn how to install Word, PowerPoint, Excel, Access, and OneNote with your free M365 subscription today. Install the latest versions of M365 apps for both Windows (PC) and Mac. Offer and access is not available to Pre-College, Continuing Education, and Seminar Students
This article is related to:
We recommend that all FIT students, faculty, and staff protect their personal computers from malicious software, inappropriate websites, and viruses by installing a high-quality antivirus program. In addition, antivirus is required for any computer trying to connect to FIT VPN. Note: don’t install additional antivirus software on any device distributed/issued by FIT even if it […]
This article is related to:
If you need to run Windows-only applications but you only have a Mac computer, Bootcamp will allow you to run Windows 10 on your Mac. Bootcamp is free for FIT students and $14.99 for Faculty and Staff. Minimum Requirements: At least 40GB free hard drive space If you do not have 40GB free on your […]
This article is related to:
It is common practice to take certain steps to protect your computer before installing new software; however, those security steps are often neglected when installing browser extensions, add-ons, social media and mobile apps. These programs may request permission to access your data; if they’re compromised by cyber attackers or if you install a malicious or […]
To log in to Brightspace, go to https://brightspace.fitnyc.edu/ in your web browser. (DO NOT add “www” to the address.)Enter your FIT Email Address and click the ‘Next’ button Enter your FIT Password and click the ‘Sign In’ buttonComplete the prompted Microsoft Multi-Factor Authentication to verify your identity
Students from approved majors that received an email inviting them to use FIT Book It will be able to make a booking. Students not in an approved major will receive a message, " Sorry! Your account does not have permission to book this item." when attempting to make a booking in FIT Book It.
This article is related to:
When you click on an email link on a web page or email message, your computer will open a new compose window with the email address populated in the To: line. The program used to compose the message is determined by the default mail client for your computer. To make Gmail your default mail client, […]
This article is related to:
What is spam? Spam is electronic junk mail. Unwanted messages sent to a large number of recipients. Why are emails marked as spam? You previously marked these messages as spam by clicking the “Report spam” or “Report phishing” button. Both actions will send the message to your Spam folder and remove it from your Inbox. […]
We are very pleased to announce that as of September 14, 2016; you will be able to use your FIT password to access your Microsoft Office 365 account, no need to manage a separate password for this service. If you are unable to sign into your Microsoft Office 365 account, please verify that you can sign into […]
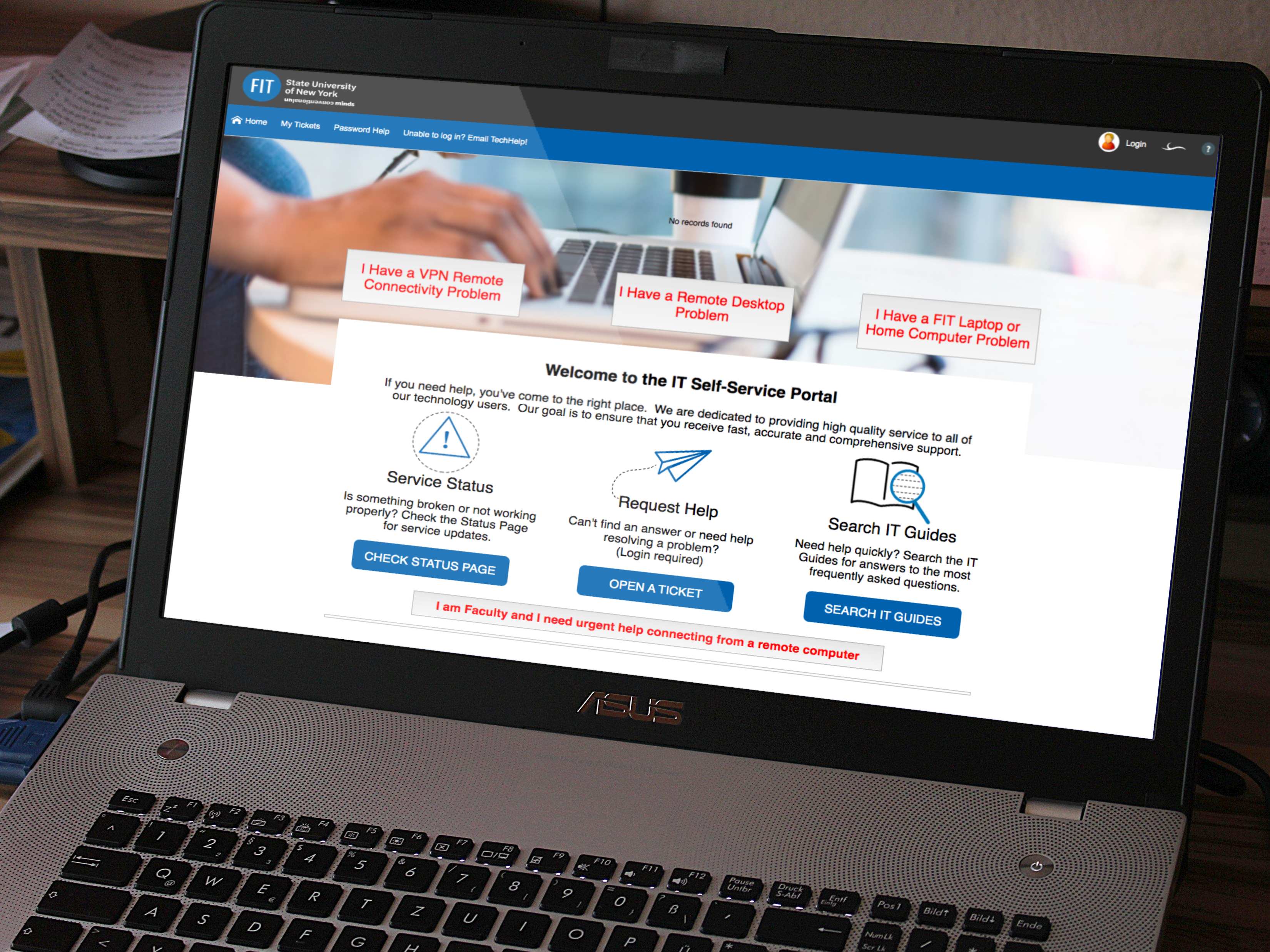
In 2019 we rolled out a new IT ticketing system including an improved self-service portal. With the self-service portal, you are able to report issues, open requests, and check their status. To use the self-service portal, go to https://TechHelp.fitnyc.edu and log in with your FIT username and password, no need to create a new login […]
Outside Student Dining Hall – Dubinsky Center Computer Commons CC15 – Feldman Center Basement Outside PrintFX - Pomerantz Center D529A FIT Library 5th Floor – Goodman Center
Click the "Register to use SSPR" button to be directed to the Self-Service Password Reset (SSPR) registration page.
Use print preview before printing and carefully select your page size, margins, layout, and pages you wish to print. Save the document you wish to print to the desktop or documents folder. DO NOT print from external storage or a web browser. Note: Files saved to local storage computer desktops and document folders are removed […]
Do Not Interact: Do not click on any links or download attachments. Do not reply to the message. 1. Forward the Email to [email protected]: Include any relevant details that may assist in the investigation. 2. Mark email as Phishing in Gmail. Click the three dots next to the reply arrow next to “Reply and then select “Report Phishing” from the […]
Reservations Suspended for Fall FIT Book It reservations end on November 25. All courses and classes will be fully remote, and students will no longer have access to campus studios and labs. After you complete a booking, you will be sent a confirmation email to your FIT email that will include an option to add […]
This article is related to:
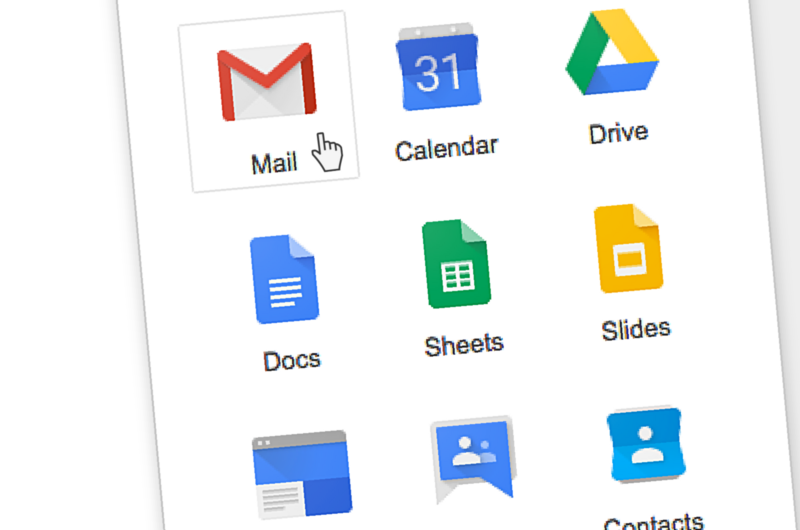
If you have more than one Google Account, you can sign in to multiple accounts at once. That way, you can switch between accounts without signing out and back in again. Please note, that the Gmail icon in MyFIT is linked to https://mail.google.com/ therefore opens to your default account or the account you are currently […]
This article is related to:
A valid FIT Username and FIT Password is required to use FIT Computers. Access to FIT Computers is only available to current FIT Students, Staff, and Faculty. Need help with a password? Visit the Password Help Center. Windows ComputerHit Ctrl + Alt + Del as instructed if the sign in window is not displayed.Enter your […]
Go to www.google.com or you can go directly to the app you wish to access; gmail.com, sheets.google.com, docs.google.com, etc.
This article is related to:
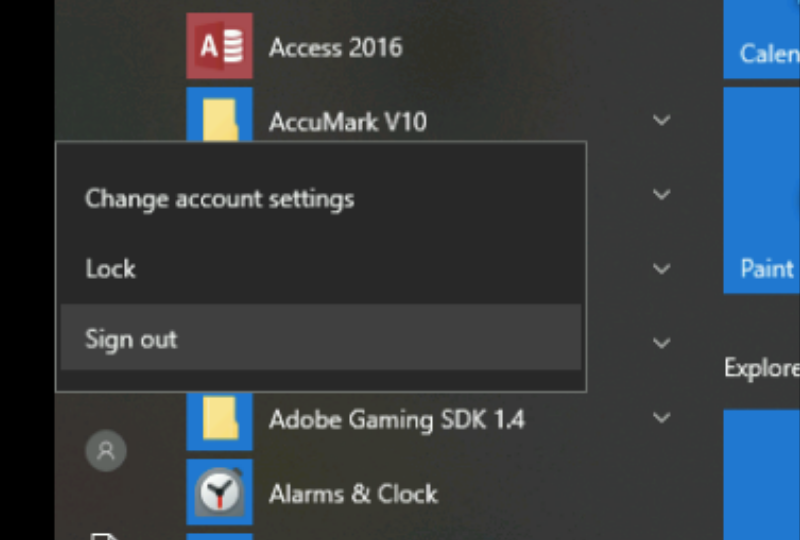
It is important to properly sign out of your computer when you are finished for the day. This is particularly important on shared devices to maintain security and make things easier for the next user. Additionally, the Division of Information Technology regularly deploys updates and system patches to fix security vulnerabilities and improve overall computer […]
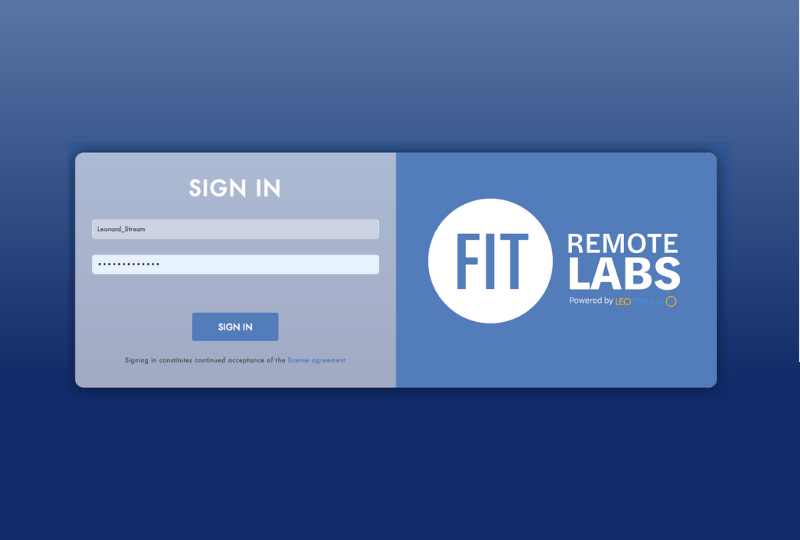
When you are finished working on your FIT Remote Labs computer or your class session is over. You must sign out properly, or you may prevent other students from accessing the computer. Do not just close the tabs, you must sign out following the instructions below.
This article is related to:
Log into your Google AccountGo to the My Account Page (https://myaccount.google.com/)Click on Device Activity and Notification
Learn how to present information while still being able to see your meeting participants. Watch the video options below or follow the step-by-step instructions for Windows or Mac in the tabs below.
IMPORTANT If you need to record or transcribe a meeting, contact the meeting organizer before the meeting so they can make you a co-host. Only the Host/Co-host with the correct subscription rights can use the recording and transcription features. How to start transcription1. Navigate to your meeting.Note : Only the host and co-hosts of the […]
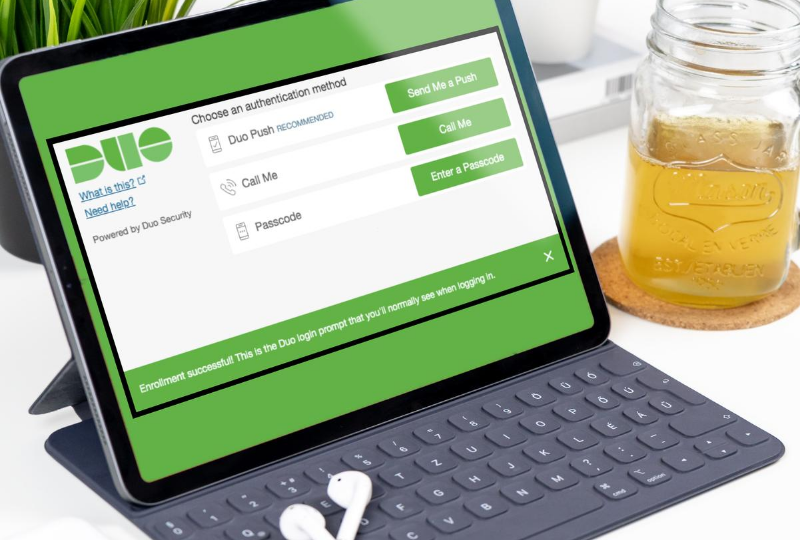
If you have not completed the DUO enrollment process, please follow our instructions on How to enroll in DUO After you enroll in Duo, each time you access FIT Remote Labs you will be presented with the screen to choose an authentication method; Send Me a Push, Call Me, or Enter a Passcode. Method/Instructions […]
This article is related to:
1. Click on the plus sign icon to Add files 2. Select “Add from Drive” 3. You can search for the meeting file or navigate to the “Meeting Recordings” folder. 4. Select transcript you want to summarize. 5. Click “Insert” 6. Enter your Prompt. Example: “Please create meeting notes from this transcript. Include attendees, a […]
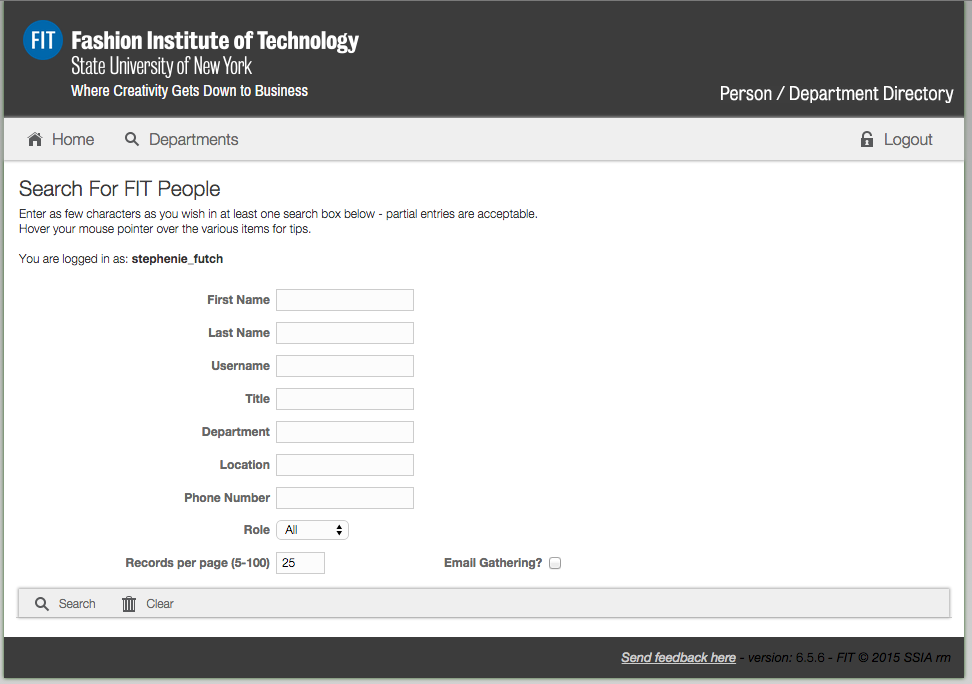
Method 1: Go directly to the online directory website at https://directory.fitnyc.edu log in with your FIT username and password. Method 2: Log in to MyFIT with your FIT username and password. Select the "Web Resources" page and then select “FIT Phone Directory” under FIT Web Resources.
When you connect your LinkedIn account, only your learning activity and profile information (name, title, profile photo) are shared with FIT LinkedIn Learning account administrators. To begin, go to https://www.linkedin.com/learning and click the “Sign in” button in the top right hand corner of the page. Enter your FIT email address and click the “Continue” button. […]
This article is related to:
Most smartphones and tablets with an active data plan from a carrier can work as mobile hotspots. A mobile hotspot provides a secure internet connection for other devices through WiFi, Bluetooth, or a USB cable.
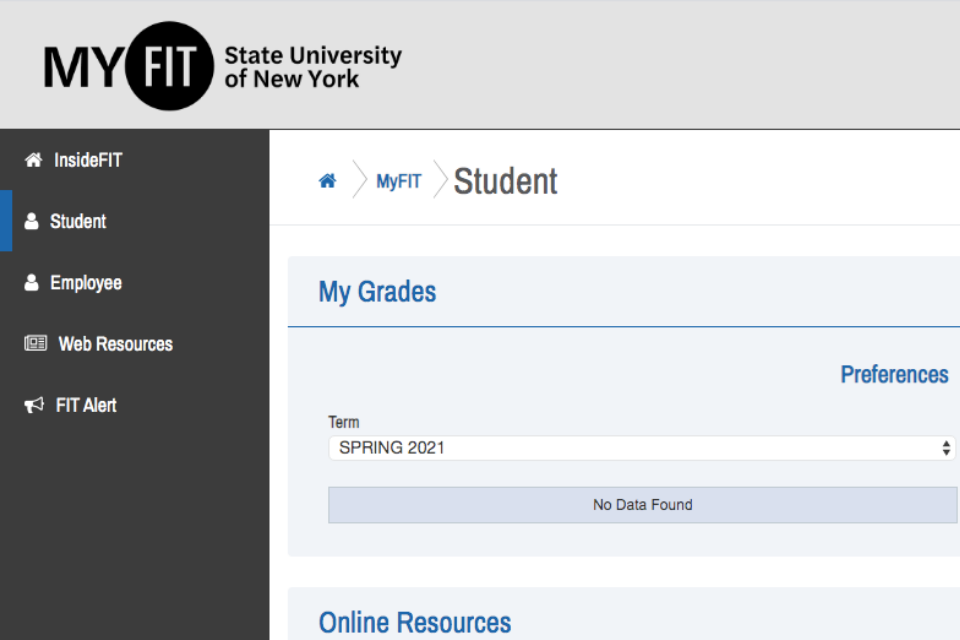
The cards in MyFIT after you sign in depend on your role or roles at FIT. You can have more than one role at FIT. Resources and cards will be available based on your role at FIT: Student High School (Pre-College) Applicant Retiree Faculty Employee – (Faculty & Staff)*An employee receives a paycheck from FIT; […]
This article is related to:
The messages below appear because OS X 10.8 and higher by default block the installation of applications that are not from the Mac App Store or created by identified developers. However, if you know the software you are installing is safe you can follow the steps below to complete the installation: Hold the Ctrl Key […]
What is an NYTimes.com Pass?NYTimes.com Passes grant digital access to The New York Times for a predefined period of time. Your access will continue until the expiration time indicated when you activate your pass. How do I activate an NYTimes.com Pass?You can activate an Academic Pass from the NYTimes.com Academic Pass page. Follow the instructions […]
What is Ransomware?Ransomware is computer malware that encrypts the files on your PC, making them (and often your whole computer) unusable. It may also encrypt files on network drives that you have access to, like your N: drive. You regain access to the files by paying a ransom to receive a decryption key. In 2016, […]
Setup your Yubico Security Key 1. In a new tab, navigate to https://mysignins.microsoft.com/security-info 2. If prompted, sign in to your account. Click on your email address if provided or enter your FIT email address Enter your FIT password, then click “Sign in” Optional click “Don’t show this again”, then click “Yes” 3. Click “Add sign-in […]
Many popular applications are available to eligible students such as Adobe and Microsoft Office at no additional cost.
Your sign in details will be provided to you by one of the following departments; please note the Division of Information Technology does not send this information. Degree ApplicantsThe Office of Admissions will send your FIT username and FIT password; after you complete the SUNY Application Online. It may take 7-10 days to receive the […]
Computer Recommendations We suggest students buy a Mac or Windows computer based on the requirements of their major and personal preferences. Please contact your major department for information about major requirements. The Division of Information Technology recommends all computers have the following minimum requirements when you buy a computer: At least 8G of RAM (*students using Creative Suite […]
Please be advised that some devices may not work on the FIT network. Many of the devices not compatible with the FIT network were designed to work in home network environments, and therefore do not fully function on a campus network environment. Many universities are experiencing the same issue with these devices. Specifically, only devices that support the […]
Your FIT ID number, sometimes called @number is a unique identification number assigned to an individual at FIT. FIT ID numbers consist of the at-sign (@) followed by eight digits. Example @01234567. To view your FIT ID number log in to MyFIT. Click on the triangle next to your name on the right-hand side of the […]
The Division of Information Technology protects our campus networks by preventing access to specific websites. We do this to guard against illegal and malicious activity on the FIT networks.