Information Security
FIT is Cybersafe is FIT’s campaign for cybersecurity for our community.
Cyberattacks, identity theft, and online scams are all over the news lately. A school might not seem like a likely target, but colleges, along with other institutions, are increasingly in the cross-hairs of global cybercriminals. College databases hold a lot of personal information about students and employees that can be valuable to hackers.
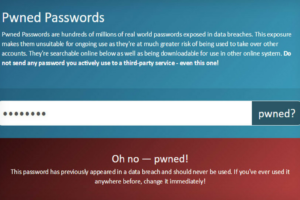
Many attacks against institutions like FIT succeed because of something a community member did (clicking on something they shouldn’t) or didn’t do (use a strong password). That’s why we’re starting a campaign to make everyone aware of what they can do to stay cybersafe. We’ll provide tips, training, and online resources and members of our security team will be at campus events to promote awareness and answer questions. And remember the same practices that protect you at FIT protect you at home.
Be aware—and Be Cybersafe!
Two Factor Authentication (2FA) at FIT
Due to the rising levels of cyberattacks that have been so visible in the media, it is important that FIT and the FIT community take the necessary steps to better protect the college and its data from cyber harm or theft.
Two-Factor Authentication (2FA) also known as 2-Step Verification, or multi-factor authentication requires a user to present two or more pieces of evidence to authenticate (verify their identity) before they are granted access to an application.

Recent Posts

Scam Alert: Beware of fake internship or job offers using FIT faculty names
More FIT students have been tricked by the latest scam/phishing emails The current scam attack is related to internship, research, or job offers that use the actual names of FIT faculty as part of the scam. Legitimate faculty and staff member emails should only come from FIT email addresses, not external ones. Any offers from […]

FIT’s 2024 Cybersecurity Training
Stay vigilant online! FIT’s 2024 Cybersecurity Training is now live. This training equips our employees with essential cyber security training to identify and combat threats and protect personal and institutional data. This mandatory training for faculty and staff is updated annually and is available through our vendor, Knowbe4. The training is 30 minutes long, […]

Cybersafe Warning – Many Cyber Scams Are Targeting Students Right Now
Email Alerts Sent We alerted the community to these scams via email on January 31, 2024 and again on February 21, 2024. Your inbox is brimming with emails from professors, organizations, and maybe even potential employers. But amid the legitimate messages, lurks a very serious hidden danger: phishing scams. What is phishing, and how can […]
Review Past Threats
Cybercriminals often reuse or create a variation of past scams, read through our threat archives to learn more about how to stay Cybersafe.